OFFER Free Microsoft 70-687 PDF and VCE Exam Dumps 201-210
Vendor: Microsoft
Exam Code: 70-687
Exam Name: Configuring Windows 8.1
Version: 14.91
QUESTION 201
You administer Windows 8.1 laptops.
The laptops are configured to connect to an unsecured wireless access point.
You plan to configure the wireless access point to encrypt wireless traffic and turn off SSID broadcast.
You need to ensure the laptops will join the secured wireless network automatically after the configuration changes.
What should you do?
A. Set Network Discovery to Enabled for the Public profile.
B. Create an ad hoc network.
C. Set the Unidentified Networks Properties User permissions to User can change location.
D. Create a network profile.
Answer: D
Explanation:
http://www.eightforums.com/tutorials/37737-wireless-network-connect-disconnect-windows-8-a.html
How to Connect To or Disconnect from a Wireless Network in Windows 8 and 8.1
Connect To a Hidden Wireless Network in Networks (Connect To)
4. Click/tap on Hidden network at the bottom. (see screenshot below)
Further Information:
http://www.7tutorials.com/how-connect-hidden-wireless-networks-windows-8
How to Connect to Hidden Wireless Networks in Windows 8
http://blogs.technet.com/b/canitpro/archive/2014/03/05/windows-8-1-tips-manage-wireless-network-profiles.aspx
Windows 8.1 tips: Managing Wireless Network Profiles
QUESTION 202
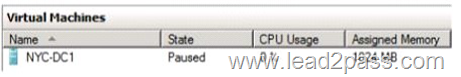
You are working with a virtual machine (VM) named NYC-DC1 on a Windows 8.1 computer.
The status of NYC-DC1 in Hyper-V Manager is shown in the following graphic.
You plan to create a snapshot of NYC-DC1.
You select the VM in Hyper-V Manager.
The Snapshot option is not available in the Actions pane or in the context menu.
You need to ensure that the Snapshot option is available.
What should you do?
A. Resume the VM.
B. Specify a location in which Hyper-V Manager should save snapshot files.
C. Save the VM.
D. Connect to the VM.
E. Increase the Assigned Memory to at least 2048 MB.
Answer: A
Explanation:
http://www.virtuatopia.com/index.php/Creating_and_Managing_Hyper-V_Snapshots
Creating and Managing Hyper-V Snapshots
What is a Hyper-V Virtual Machine Snapshot?
yper-V virtual machine snapshots allow the status of a virtual machine (and the corresponding guest operating system) at a particular time to be saved such that it can be reverted to that state at any point in the future. Hyper-V snapshots contain both the configuration settings of the virtual machine, and the state of the guest operating system at the point the snapshot is taken. Snapshots may be taken of virtual machines when they are running, stopped or saved. It is not possible, however, to take a snapshot of a paused Hyper-V virtual machine.
When a snapshot is taken of a saved or running virtual machine, the snapshot contains the status of both the file system and the memory used by the guest operating system. As such, when the virtual machine is reverted to the snapshot everything, including applications running at the time the snapshot was taken, will be restored to the snapshot status.
Virtual machines are reverted to a snapshot status by applying the desired snapshot to the virtual machine.
QUESTION 203
You administer client computers in your company network.
The network includes an Active Directory Domain Services (AD DS) domain.
Employees in the human resources (HR) department are getting new Windows 8.1 Enterprise computers. The HR department uses a line of business (LOB) Windows Store app named Timesheet that is not available in Windows Store.
You need to ensure that all employees in the HR department can use Timesheet on their new computers.
What should you do?
A. Use a local account to log on to each computer.
B. Set the Turn off the Store application group policy to Enabled.
C. Activate the sideloading product key on each computer.
D. Set the Allow Store to install apps on Windows To Go workspaces group policy setting to Enabled.
Answer: C
Explanation:
* The average Windows 8 user can only download apps that Microsoft has approved from the Windows Store. Windows 8 offers two ways to sideload unapproved apps, which are intended for developers and businesses with internal apps.
* Windows 8 offers a method for sideloading "line-of-business" apps. This allows businesses and other organizations to load apps onto their own computers without offering them publically through the Windows Store.
There are four requirements to sideload a line-of-business app:
You must be using Windows 8 Enterprise, Windows Server 2012, Windows 8 Pro, or Windows RT. If you’re using Windows 8 Pro or Windows RT, you’ll need to purchase a "sideloading product activation key" from Microsoft.
QUESTION 204
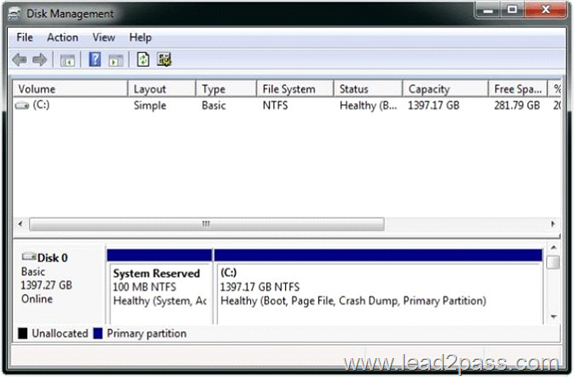
A company has 10 client computers that run Windows 7.
All client computers have the same hardware configuration. The hardware configuration includes custom hardware components manufactured by the company.
The computer hard drives are configured as shown in the Disk Management window exhibit. (Click the Exhibit button.)
The company plans to upgrade the client computers to Windows 8.1.
You need to test hardware compatibility with Windows 8.1 on one client computer and leave the existing Windows 7 installation intact.
Which two actions should you perform? (Each correct answer presents part of the solution.
Choose two.)
A. Insert the Windows 8 installation media into the computer, and then run the Setup program.
B. Shrink the current hard drive partition, and then create a new partition for the Windows 8 installation.
C. Change the hard drive to a dynamic disk and create a new dynamic volume.
D. Start the computer from the Windows 8 installation media and then select the Custom installation option.
Answer: BD
Explanation:
http://windows.microsoft.com/en-us/windows/install-multiple-operating-system-multiboot#1TC=windows-7
If your computer’s hard disk has adequate free disk space, you can install a newer version of Windows on a separate partition and keep the earlier version of Windows on your computer.
This is called a multiboot or dual-boot configuration.
Whenever you start your computer, you can then choose which version of Windows to run.
Multibooting requires separate partitions on your computer’s hard disk for each operating system.
Example of a multiboot disk configuration
QUESTION 205
You administer Windows 8.1 Pro computers in your company network.
A user named User1 encrypts a sensitive file named file.txt by using Encrypting File System (EFS).
A user named User2 must be able to read file.txt.
You need to configure unencrypted read access to file.txt for User2.
What should you do?
A. Configure Advanced Security Settings.
B. Share the folder that contains file.txt.
C. Configure Advanced Attributes.
D. Configure Effective Access.
Answer: C
Explanation:
http://www.howtogeek.com/178912/how-to-encrypt-files-and-folders-in-windows-8.1-using-efs/
QUESTION 206
You use a Windows 8.1 laptop.
You want to back up the Pictures library.
You need to configure a backup strategy that backs up the Pictures library to a network drive every day. Additionally, you need to be able to recover a copy of any files from the library that have been changed within the last month.
What should you do?
A. Create a system image.
B. Configure File History.
C. Create a Storage Pool.
D. Configure computer restore points.
Answer: B
Explanation:
http://blogs.msdn.com/b/b8/archive/2012/07/10/protecting-user-files-with-file-history.aspx Protecting user files with File History
File History is a backup application that continuously protects your personal files stored in Libraries, Desktop, Favorites, and Contacts folders. It periodically (by default every hour) scans the file system for changes and copies changed files to another location. Every time any of your personal files has changed, its copy will be stored on a dedicated, external storage device selected by you. Over time, File History builds a complete history of changes made to any personal file.
As described above, to start protecting your libraries, you need to attach an external drive or select a network location. File History will store versions of your files on this device.
QUESTION 207
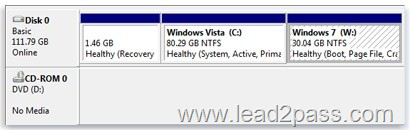
A company has client Windows Vista and Windows 8.1.
You need to ensure that the client computers can share local resources.
Which two actions should you perform on the client computers? (Each correct answer presents part of the solution. Choose two.)
A. Disable IPv6.
B. Enable network discovery.
C. Configure IPSec.
D. Enable IPv6.
E. Configure the Windows Firewall.
Answer: BE
Explanation:
By changing your network location to Home or Work, network discovery is automatically turned on. You can also turn on these sharing options individually:
Network discovery
File sharing (in Windows 7, this is automatically turned on when you share a file or folder) Public folder sharing
When you turn on these options, your computer can:
Find other computers and devices on your home network and have other computers find your computer
Share its files and folders
Share its Public folders
QUESTION 208
You administer Windows 8.1 client computers in your company network. The company has an Active Directory Domain Services (AD DS) domain named contoso.com. The domain contains a domain controller configured to lease DHCP and DHCPv6 addresses.
A client computer named Computer1 is configured to obtain IPv4 and IPv6 addresses automatically.
A user reports that an IPv6-enabled application named Appl is not working on Computer1.
You discover that Computer1 has an IPv6 address prefix of FE80::. You are able to ping Computer1 successfully by using IPv4, but when you use IPv6, your ping requests time out.
You need to ensure that Computer1 will support Appl.
Which command should you use?
A. jpconfig /allcompartments /all
B. jpconfig /renew
C. jpconfig /renew6
D. jpconfig /release6
Answer: C
Explanation:
http://en.wikipedia.org/wiki/Link-local_address
Link-local address
In a computer network, a link-local address is a network address that is valid only for communications within the network segment (link) or the broadcast domain that the host is connected to.
Link-local addresses are usually not guaranteed to be unique beyond a single network segment. Routers therefore do not forward packets with link-local addresses.
Link-local addresses for IPv4 are defined in the address block 169.254.0.0/16, in CIDR notation. In IPv6, they are assigned with the FE80::/10 prefix.
http://technet.microsoft.com/en-us/library/dd197434.aspx Ipconfig
Displays all current TCP/IP network configuration values and refreshes Dynamic Host Configuration Protocol (DHCP) and Domain Name System (DNS) settings. Used without parameters, ipconfig displays Internet Protocol version 4 (IPv4) and IPv6 addresses, subnet mask, and default gateway for all adapters.
Syntax
ipconfig [/allcompartments] [/all] [/renew [<Adapter>]] [/release [<Adapter>]]
[/renew6[<Adapter>]] [/release6 [<Adapter>]] [/flushdns] [/displaydns] [/registerdns] [/showclassid <Adapter>] [/setclassid <Adapter> [<ClassID>]]
Parameters
/allcompartments
Displays the full TCP/IP configuration for all compartments.
/renew [<Adapter>]
Renews DHCP configuration for all adapters (if an adapter is not specified) or for a specific adapter if the Adapter parameter is included. This parameter is available only on computers with adapters that are configured to obtain an IP address automatically. To specify an adapter name, type the adapter name that appears when you use ipconfig without parameters.
/renew6 [<Adapter>]
Renews DHCPv6 configuration for all adapters (if an adapter is not specified) or for a specific adapter if the Adapter parameter is included. This parameter is available only on computers with adapters that are configured to obtain an IPv6 address automatically. To specify an adapter name, type the adapter name that appears when you use ipconfig without parameters.
/release6[<Adapter>]
Sends a DHCPRELEASE message to the DHCPv6 server to release the current DHCP configuration and discard the IPv6 address configuration for either all adapters (if an adapter is not specified) or for a specific adapter if the Adapter parameter is included. This parameter disables TCP/IP for adapters configured to obtain an IP address automatically. To specify an adapter name, type the adapter name that appears when you use ipconfig without parameters.
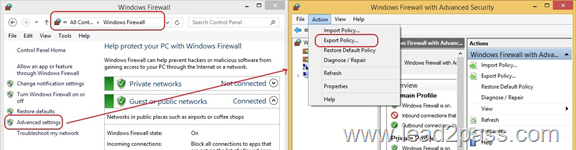
QUESTION 209
You administer Windows 8.1 Enterprise client computers in your company network.
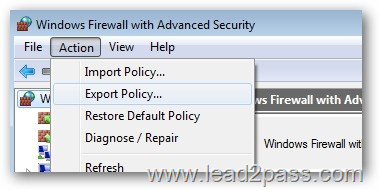
You change settings on a reference computer by using the Windows Firewall with Advanced Security tool.
You want to apply the same settings to other computers.
You need to save the Windows Firewall with Advanced Security configuration settings from the reference computer.
You also need to be able to import the configuration settings into a Group Policy object later.
What should you do?
A. Run the netsh advfirewall export c:\settings.xml command.
B. Open Local Group Policy Editor, select the Windows Firewall with Advanced Security node, and
then select the Export Policy action.
C. Open Local Group Policy Editor, select the Security Settings node, and then select the Export List action.
D. From Control Panel, open Windows Firewall, click Advanced Settings, and then select the Export Policy action.
Answer: D
Explanation:
The export netsh file format is wfw, not .xml . Also, the export works just fine from the "Advanced Settings", which actually launches the full fledged Windows Firewall with Advanced Security:
http://www.howtogeek.com/100409/group-policy-geek-how-to-control-the-windows-firewall-with-a-gpo/
Group Policy Geek: How to Control the Windows Firewall With a GPO
Exporting the Policy
To export the policy, in the left hand pane click on the root of the tree which says Windows Firewall with Advanced Security. Then click on Action and select Export Policy from the Menu
You should save this to either a network share, or even a USB if you have physical access to your server. We will go with a network share.
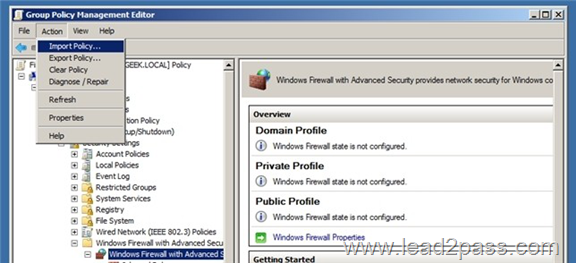
Importing the Policy Into Group Policy
To import the firewall policy you need to open an existing GPO or create a new GPO and link it to an OU that contains computer accounts
Now navigate to:
Open Computer Configuration\Policies\Windows Settings\Security Settings\Windows Firewall with Advanced Security
Click on Windows Firewall with Advanced Security and then click on Action and Import Policy
You will be told that if you import the policy it will overwrite all existing settings, click yes to continue and then browse for the policy that you exported in the previous section of this article. Once the policy has finished being Imported you will be notified.
QUESTION 210
A company has an Active Directory Domain Services (AD DS) domain.
All client computers run Windows 8.1 and are joined to the domain.
An employee is unable to connect his portable client computer to his home office homegroup.
You need to ensure that the network adapter settings of the client computer support joining a homegroup.
What should you do?
A. Disable IPv6.
B. Enable IPv4.
C. Enable IPv6.
D. Disable IPv4.
Answer: C
Explanation:
http://social.technet.microsoft.com/wiki/contents/articles/4515.homegroup-and-ipv6- troubleshooting-guide.aspx
HomeGroup and IPv6 Troubleshooting Guide
Your router and all computers must be IPv6 capable (hardware, firmware, and drivers) to use HomeGroup.
If you want to pass Microsoft 70-687 exam successfully, donot missing to read latest lead2pass Microsoft 70-687 dumps.
If you can master all lead2pass questions you will able to pass 100% guaranteed.
http://www.lead2pass.com/70-687.html
Why Choose Lead2pass?
If you want to pass the exam successfully in first attempt you have to choose the best IT study material provider, in my opinion, Lead2pass is one of the best way to prepare for the exam.
 |
 |
 |
 |
 |
|
|---|---|---|---|---|---|
 |
 |
 |
 |
 |
|
| Lead2pass | Testking | Pass4sure | Actualtests | Others | |
| $99.99 | $124.99 | $125.99 | $189 | $29.99-$49.99 | |
| Up-to-Dated | ✔ | ✖ | ✖ | ✖ | ✖ |
| Real Questions | ✔ | ✖ | ✖ | ✖ | ✖ |
| Error Correction | ✔ | ✖ | ✖ | ✖ | ✖ |
| Printable PDF | ✔ | ✖ | ✖ | ✖ | ✖ |
| Premium VCE | ✔ | ✖ | ✖ | ✖ | ✖ |
| VCE Simulator | ✔ | ✖ | ✖ | ✖ | ✖ |
| One Time Purchase | ✔ | ✖ | ✖ | ✖ | ✖ |
| Instant Download | ✔ | ✖ | ✖ | ✖ | ✖ |
| Unlimited Install | ✔ | ✖ | ✖ | ✖ | ✖ |
| 100% Pass Guarantee | ✔ | ✖ | ✖ | ✖ | ✖ |
| 100% Money Back | ✔ | ✖ | ✖ | ✖ | ✖ |